Get in Touch
Get in Touch
Our Services
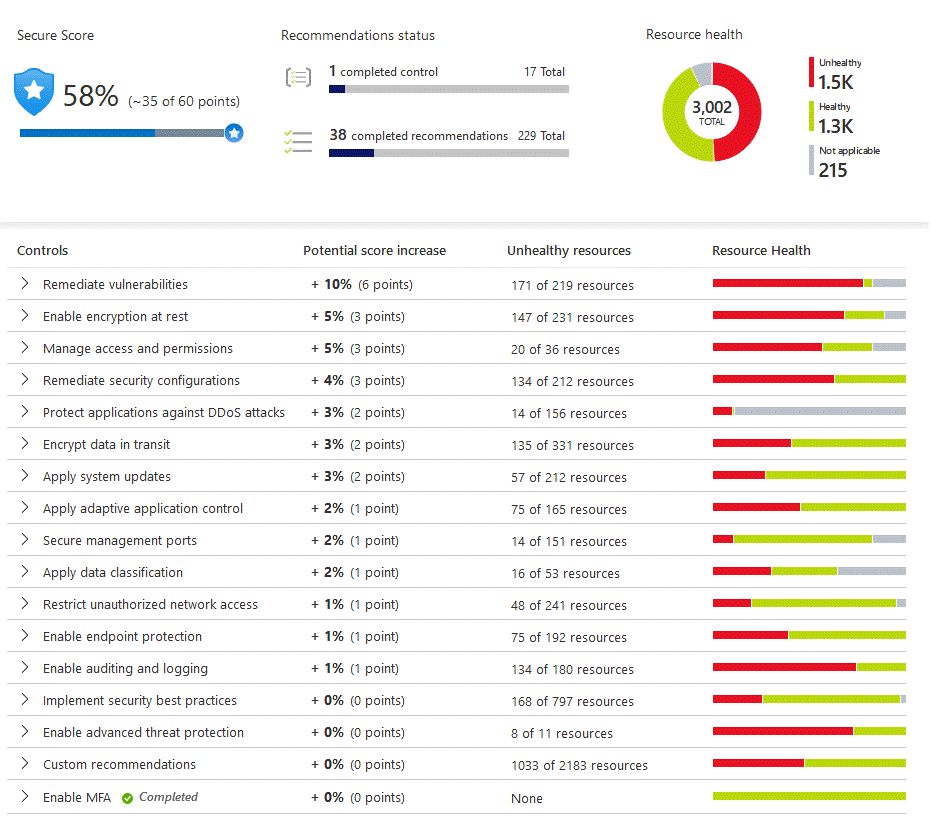
CyberSoC Capital uses a wide variety of physical, infrastructure, and operational controls to help secure Azure-but there are additional actions you need to take to help safeguard your workloads. We use Azure Security Center to strengthen your cloud security posture. Within Azure Security Center, use Azure Defender to protect your hybrid cloud workloads.
Strengthen the security posture of cloud workloads
Assess the security state of all your cloud resources, including servers, storage, SQL, networks, applications, and workloads that are running in Azure, on-premises, and in other clouds. Visualize your security state and improve your security posture by using Azure Secure Score recommendations. View your compliance against a wide variety of regulatory requirements or company security requirements by centrally managing security policies. Perform ongoing assessment and get rich, actionable insights and reports to simplify compliance.

CyberSoC Capital uses Azure Security Center which is a unified infrastructure security management system that strengthens the security posture of your data centers, and provides advanced threat protection across your hybrid workloads in the cloud - whether they're in Azure or not - as well as on premises.
Keeping your resources safe is a joint effort between your CyberSoC Capital, Azure, and you. We help ensure your workloads are secure as you move to the cloud, and at the same time, when you move to IaaS (infrastructure as a service) there is more CyberSoC Capital responsibility than there was in PaaS (platform as a service), and SaaS (software as a service). CyberSoC Capital uses Azure Security Center to provide you the tools needed to harden your network, secure your services and make sure you're on top of your security posture.

- Rapidly changing workloads :- It's both a strength and a challenge of the cloud. On the one hand, end users are empowered to do more. On the other, how do you make sure that the ever-changing services people are using and creating are up to your security standards and follow security best practices?
- Increasingly sophisticated attacks :- Wherever you run your workloads, the attacks keep getting more sophisticated. You have to secure your public cloud workloads, which are, in effect, an Internet facing workload that can leave you even more vulnerable if you don't follow security best practices.
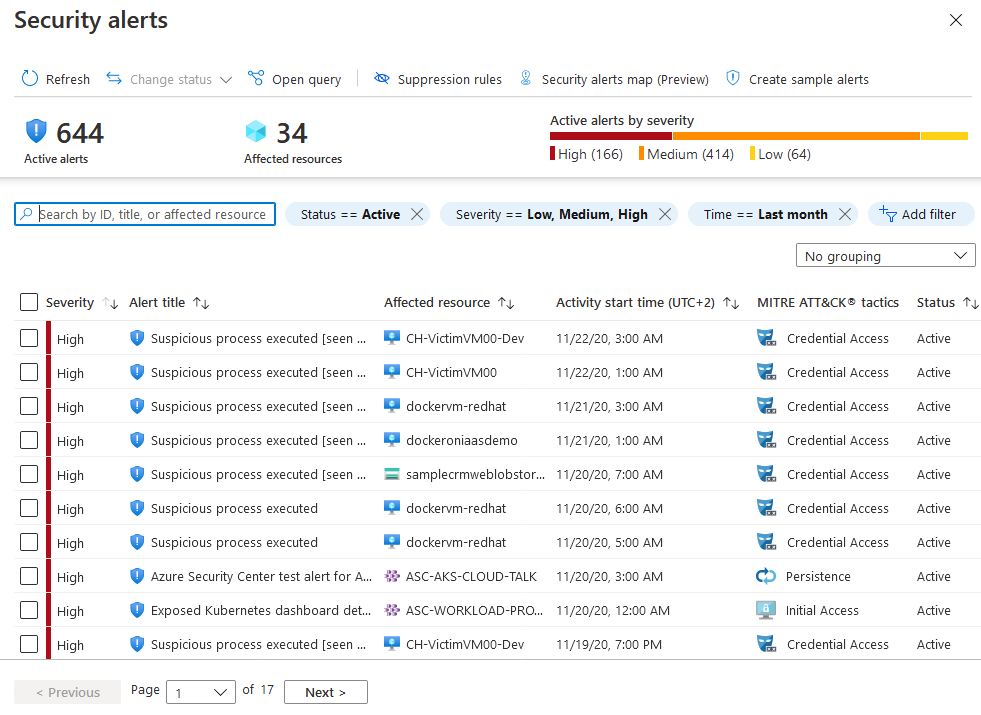
- Security skills are in short supply :- The number of security alerts and alerting systems far outnumbers the number of administrators with the necessary background and experience to make sure your environments are protected. Staying up-to-date with the latest attacks is a constant challenge, making it impossible to stay in place while the world of security is an ever-changing front.
To help you protect yourself against these challenges, CyberSoC Capital provides you with the tools to :-
- Strengthen security posture :- Security Center assesses your environment and enables you to understand the status of your resources, and whether they are secure.
- Protect against threats :- Security Center assesses your workloads and raises threat prevention recommendations and security alerts.
- Get secure faster :- In Security Center, everything is done in cloud speed. Because it is natively integrated, deployment of Security Center is easy, providing you with auto provisioning and protection with Azure services.
Capabilities :-
Integration with Microsoft Defender for Endpoint
Azure Defender for servers includes automatic, native integration with Microsoft Defender for Endpoint. Learn more, Protect your endpoints with Security Center's integrated EDR solution: Microsoft Defender for Endpoint.
Protect PaaS
Security Center helps you detect threats across Azure PaaS services. You can detect threats targeting Azure services including Azure App Service, Azure SQL, Azure Storage Account, and more data services. You can also take advantage of the native integration with Microsoft Cloud App Security's User and Entity Behavioral Analytics (UEBA) to perform anomaly detection on your Azure activity logs.
Block brute force attacks
Security Center helps you limit exposure to brute force attacks. By reducing access to virtual machine ports, using the just-in-time VM access, you can harden your network by preventing unnecessary access. You can set secure access policies on selected ports, for only authorized users, allowed source IP address ranges or IP addresses, and for a limited amount of time.
Protect data services
Security Center includes capabilities that help you perform automatic classification of your data in Azure SQL. You can also get assessments for potential vulnerabilities across Azure SQL and Storage services, and recommendations for how to mitigate them.
Get secure faster
Native Azure integration (including Azure Policy and Azure Monitor logs) combined with seamless integration with other Microsoft security solutions, such as Microsoft Cloud App Security and Microsoft Defender for Endpoint help make sure your security solution is comprehensive as well as simple to onboard and roll out.
In addition, you can extend the full solution beyond Azure to workloads running on other clouds and in on-premises data centers.
Automatically discover and onboard Azure resources
Security Center provides seamless, native integration with Azure and Azure resources. That means that you can pull together a complete security story involving Azure Policy and built-in Security Center policies across all your Azure resources, and make sure that the whole thing is automatically applied to newly discovered resources as you create them in Azure.
Extensive log collection - logs from Windows and Linux are all leveraged in the security analytics engine and used to create recommendations and alerts.